
Identity theft and account takeover are on the rise, with cyberattacks targeting the financial sector increasing 238% from February to April 2020, according to a VMware Carbon Black report.
Now more than ever, as businesses deal with the financial stressors of the global health and economic crisis brought on by COVID-19, there has never been a more crucial time to establish trust between organizations and consumers. Online ID verification is a great starting point in building trust, but how do you really know who is holding that ID on the other end?
Defining ID and Identity Verification
Most organizations use some method of identity verification during the digital onboarding process. Some ping databases to see if an individual exists in the real world. Some use ID verification to check the authenticity of a user’s government-issued ID and to ensure it has not been digitally manipulated. ID verification provides a strong trust anchor for online businesses, but it fails to assure that the user holding the ID is in fact who they say they are.
Online identity verification takes the verification process one step further and involves both an ID scan and the capture of a corroborating selfie to ensure that the person holding the ID is the same person shown in the ID photo and that they are physically present during the transaction. In this way, identity verification serves many benefits to organizations seeking to build trust in their online channels.
5 Ways it Pays to Go Beyond the ID
So, what are five ways identity verification can add real value to your organization?
1. Fraud Deterrence
The addition of a selfie requirement and liveness detection has a chilling effect on online fraud and account takeover. The simple act serves as a strong fraud deterrent for many scammers who prefer not to share their own likeness with the company they’re looking to defraud and reduces attempted fraud attempts by as much as 90% (based on Jumio’s benchmark analysis).
2. Simple and Familiar User Experience
Two-thirds (67%) of consumers are comfortable using biometric authentication today, while 87% say they’ll be comfortable with these technologies in the near future, according to IBM. Thanks to the broad adoption and familiarity of facial recognition integrated within the most popular smartphones – think Apple Face ID and Samsung’s facial recognition feature – this trend is rapidly increasing.
3. Security Checks
With identity verification, we go one step beyond ID verification by conducting a variety of security checks to verify that the user’s selfie matches the photo on the government-issued ID, and that the selfie is real.
4. Certified Liveness Detection
Given the rise of spoofing (the act of using a photo, video or a different substitute in lieu of an actual selfie), Jumio employs state-of-the-art 3D liveness detection to ensure that a new customer is physically present when creating their online account.
5. Higher Levels of Assurance
Online identity verification delivers a much higher level of identity assurance compared to traditional methods of identity verification such as knowledge-based verification, credit-bureau pings and database solutions that are no longer reliable/secure thanks to large-scale data breaches, the dark web and other sophisticated hacking techniques (e.g., SIM swap fraud, man-in-the-middle attacks).
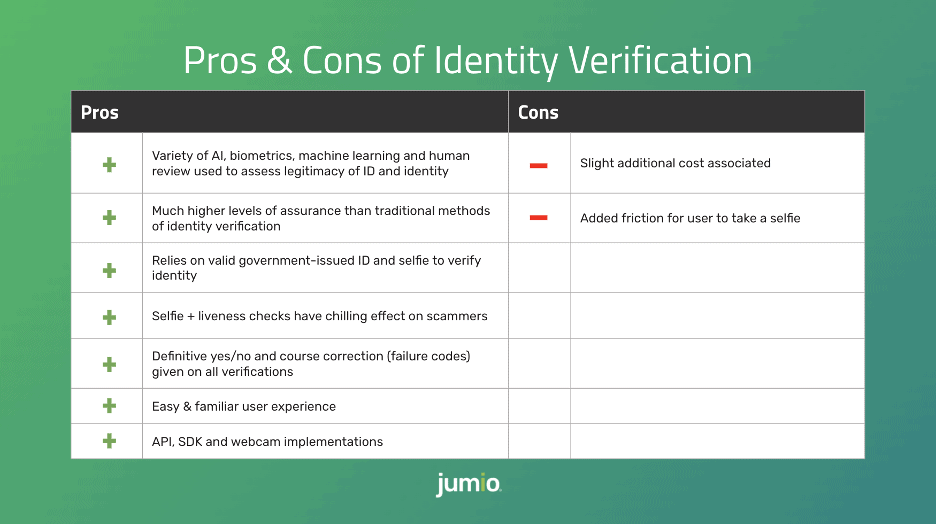
Pros and Cons of Identity Verification
The challenge that organizations face is to create a seamless identity verification process while simultaneously reducing friction and deterring fraud. The pros of Jumio’s online identity verification certainly outweigh the cons and can help organizations easily verify their users online in seconds and help companies improve conversion rates, comply with AML and KYC regulations and better detect fraud.
Now is the time to take the next step in your online verification process with AI-powered identity verification. If you’re looking for a verification process with higher assurance — especially for organizations dealing with high-risk transactions and sensitive information or operating in regulated industries (where the cost of non-compliance can be costly) — the choice is clear to go beyond ID verification and take the next step with identity verification.