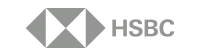
Design powerful, risk-based workflows.
Create workflows that fit your exact business needs while providing a best-in-class experience for end users. Dynamically trigger the right checks at the right time, introducing friction only for higher-risk individuals. Start with our expert rules library, then refine and customize them in the editor powered by our advanced engine to align with your unique risk strategy.

Decision-making aligned to your business.
Jumio calculates a single risk score based on numerous risk signals set to your business specifications, triggering additional assessments as needed. Expedite and simplify decision-making by aligning processes with your organization’s growth strategy and risk tolerance.

Maximize visibility and efficiency with user-friendly reporting.
Turn identity intelligence into action with configurable reports focused on trends, conversion, fraud types, customized metrics, and more, from Jumio’s streamlined dashboard. Empower leadership and teams to make informed decisions at the speed of business.
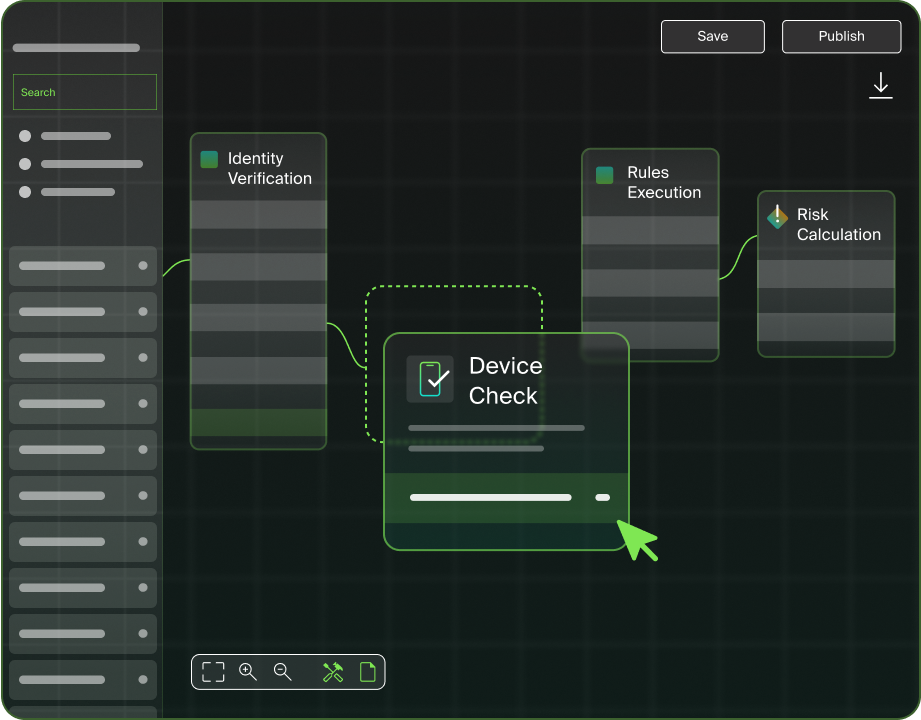
Seamless integration on your terms.
Take full control with APIs and SDKs to customize and host the user journey within your existing framework, including mobile-native experience for iOS and Android. Or get up and running effortlessly with Jumio’s web client, where you can embed a default user journey as a web app across any device.
End-to-end Identity Intelligence
Powered by leading-edge innovation.
This is identity that thinks.
Identity inteligence. Jumio Smart.
See how our clients are growing their businesses with Jumio.
VP of Digital Experience Alaska Airlines