There’s a healthy degree of confusion between facial recognition and facial authentication, but the underlying technologies are often very different and designed to address different use cases. With the launch of Apple iPhone X and its successors, facial recognition has gone mainstream and helped consumers recognize that their faces could serve as their password.
In this post, we will compare and contrast facial recognition and facial authentication and provide some cautions to companies considering facial recognition systems in commercial use cases when facial authentication is more appropriate, reliable and secure.
What is Facial Recognition vs. Facial Authentication?
Let’s start with some basics:
Facial Recognition: A biometric software application capable of uniquely identifying or verifying a person by comparing and analyzing patterns based on the person’s facial contours.
Facial Authentication: A form of biometric authentication that relies on the unique biological characteristics of an individual to verify that she is who she claims to be.
While both leverage biometric authentication and both are used to verify individuals, they differ in some pretty fundamental ways. First, let’s explore facial recognition.
What’s Facial Recognition Technology Used For?
Apple deservedly gets much of the credit for making this technology available to common people in day-to-day life and for elevating the face as the most reliable, natural and secure biometric compared to its predecessors like fingerprint, IRIS sensors and voice recognition.
But, the use of facial recognition in real-time goes well beyond unlocking your phone. In fact, facial recognition technology is being leveraged within the United States and around the world, mostly for security purposes, and is increasingly being adopted for a wide range of applications, including:
- Retail: Face recognition is being used to instantly identify when known shoplifters, organized retail criminals or people with a history of fraud enter retail establishments.
- Law Enforcement: Facial recognition is already helping law enforcement agencies from the FBI to local police departments instantly identify individuals in the field from a safe distance. This intel can provide contextual data that tells them whether they need to proceed with caution.
- Advertising: Facial recognition is enabling more targeted advertising by making educated guesses at people’s age and gender. Companies like Tesco are already planning on installing screens at gas stations with facial recognition built in.
- School Safety: Facial recognition surveillance systems can instantly identify when dangerous parents, expelled students, drug dealers or other individuals that pose a threat to school safety enter school grounds.
- Missing Persons: Facial recognition can be used to find missing children and victims of human trafficking. As long as missing individuals are added to a database, law enforcement can become alerted as soon as they are recognized by facial recognition — be it an airport, retail store or other public space.
- Social Media: Facebook uses face recognition technology to automatically recognize when its members appear in photos. This makes it easier for people to find photos of themselves and can suggest when particular people should be tagged in photos.
- Casinos: Facial recognition helps casinos recognize the moment that a known cheater or member of voluntary exclusion lists enter a casino — these players can cost casinos hefty fines if they’re caught gambling.
- Financial Services: A more concerning use of facial recognition (for reasons that will be enumerated below) has been in the financial services arena where facial recognition is being used for digital payments, account opening and online account access.
Achieve End-to-End Identity Verification and Authentication in Today’s Digital World
The Collision of Identity Proofing & Authentication
How Face Recognition Systems Work
Facial recognition is a way of recognizing a human face through technology. Modern facial recognition software use biometrics to map facial features from a photograph or video. It then compares the information with a database of known faces to find a match.
While technologies vary, here’s how facial recognition works:
Step 1: A picture of a face is captured from a photo or video.
Facial recognition analyzes an individual’s face within the context of their surroundings. A face might appear alone or in a crowd and may show the face in profile or looking straight ahead.
Step 2: Facial geometry analysis
Facial recognition software analyzes images of people’s faces based on factors such as distance between your eyes and the distance from forehead to chin. The software creates a facial signature based on facial landmarks that distinguish one face from another.
Step 3: Facial signatures compared
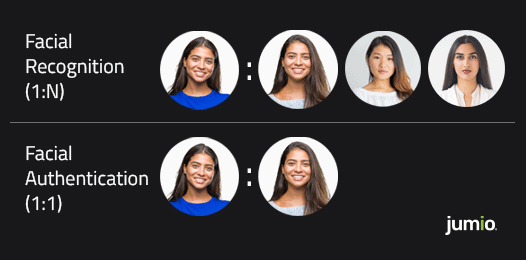
The facial signature (which is really just a mathematical algorithm) is compared to a database of known faces. This is what is known as 1:n matching (where n equals the number of face signatures in a database).
Step 4: Match/no match decision
A match/no match determination is made based on whether the faceprint captured matches that of an image in a facial recognition system database.
Facial recognition software is by no means foolproof. Facial recognition accuracy can vary significantly based on a wide range of factors, such as camera quality, light, distance, database size, algorithm and the subject’s race and gender (more on those last key factors in a second). Highly advanced systems can generally have false positive error rates (i.e., the system erroneously declares a match) below 10 percent.
Limitations of Facial Recognition
Facial recognition is ideal for matching a photo against large datasets of other facial images or videos, or comparing a high-quality selfie against another high-quality selfie. But facial recognition is not ideal for other use cases where a more definitive match is required. These scenarios include:
- Identity Proofing: Facial recognition software is not designed for matching a selfie to a low-quality photo on a driver’s license or passport — a process that is often used for online identity verification. Pictures on ID documents are of notoriously poor quality and often small, grayscale and overexposed. Plus, the physical characteristics of people change over time — they may gain weight, lose their hair, grow a beard or start wearing glasses — which makes comparing a recent selfie to an older low-resolution ID picture difficult.
- Criminal Consequences: While a 90 percent accuracy rate may sound good in general, it is an unacceptable risk when the end result is the possible arrest of or even use of force (including deadly force) against an innocent person. That’s why many experts say facial recognition should stay out of law enforcement’s hands until it becomes more accurate.
- Liveness Detection: Another shortcoming of facial recognition software is that it cannot definitively assess the digital identity of an online user or assess whether they’re physically present. Sadly, cybercriminals are using spoofing attacks to outsmart biometric systems by using a photo, video or a different substitute for an authorized person’s face.
Now, let’s turn our attention to facial authentication.
The Power and Application of Facial Authentication
Facial authentication is the process of determining whether someone or something is, in fact, who or what it declares itself to be. After an online user has been vetted through some identity proofing or verification process, they are usually given a unique credential (i.e., username and password combination) that lets the user access their online account or perform certain actions. The verification of those credentials is what we call authentication.
How Facial Authentication Works
Unlike facial recognition which performs a 1:n match against a database of known faces, facial authentication is 1:1. The user is authenticating using their face as their credential to secure access to their online account. To authenticate, the user simply takes a selfie, from which a biometric template is created and compared, one-to-one, with the stored biometric template. A proper match, based on an accuracy score, completes the secure authentication process in the background.
The facial authentication process follows these basic steps as part of an identity proofing procedure:
Step 1: Capture a picture of a government-issued ID document
This step requires the user to capture a picture of a government-issued ID (e.g., a driver’s license or passport).
Step 2: Take a corroborating selfie
To ensure that the ID document belongs to the actual person and wasn’t stolen, identity proofing requires the user to take a selfie which is then compared to the picture on the ID document. This step has a chilling effect on fraudsters who generally don’t want to use their own image and share it with the organization they’re looking to defraud.
Step 3: Perform a liveness check
Part of the selfie-taking process includes a test for liveness to ensure that the user is physically present during the transaction. This is done to better thwart fraudsters who are increasingly using spoofing attacks by using a photo, video or a different substitute for an authorized person’s face to acquire someone else’s privileges or access rights.
Step 4: Create a biometric template
During the liveness check and selfie-taking process, a biometric template is created. Similar to a facial signature, this template is an algorithm that is unique to the user and it’s this template that is stored by the business customer for future authentication events.
Step 5: Issue login credentials (if approved)
The user is vetted by the company and issued login credentials if successfully verified.
Step 6: Confirm the user’s digital identity
When the user needs to log into their account or perform a high-risk transaction (e.g., a wire transfer or password reset), the user is asked to retake a selfie. A new biometric template is created and compared with the one created during the initial enrollment and a match/no match decision is made in seconds.
Step 7: Learn from itself
Better facial authentication solutions will learn from each authentication event in a process known as adaptive learning. This means the new biometric template is compared not only to the original face map but all subsequent face maps to improve authentication accuracy and reliability.
See how Jumio simplifies facial authentication here:

Benefits of Facial Authentication
Unfortunately, traditional authentication methods, such as SMS-based two-factor authentication and knowledge-based authentication, are no longer considered best practices because of reliability and security concerns such as phishing attacks and man-in-the-browser exploits.
That’s why modern online companies are also increasingly looking for facial authentication solutions that more reliably establish the online identity of new customers (during the account setup process) and existing users for authentication events — especially high-risk transactions such as wire transfers or password resets.
There are a number of tangible advantages of facial authentication over traditional authentication methods.
Better Identity Assurance
By requiring a valid government-issued ID and matching it to a selfie (with certified liveness detection), enterprises can have a much higher level of assurance that the person is who they claim to be.
Easier for Users
Thanks to the popularity of Apple’s Face ID, facial authentication has become more familiar and accepted. When combined with certified anti-spoofing capabilities, biometric-based authentication improves the user experience and reduces friction because of its ease of use, speed and omnichannel support (across mobile devices and webcams).
Stronger Fraud Detection
How well can the solution detect malware, bots and bad actors? Companies need to be able to confidently assess risk and make more informed application-processing decisions while minimizing fraud loss. Companies also need to better detect identity theft, account takeover and synthetic fraud — some of the largest threats facing online organizations today.
Need for Speed
While most users are willing to endure a bit of friction when creating an online account, they’re increasingly demanding authentication solutions that are fast, simple and reliable. Modern facial authentication can now quickly compare a new selfie to a previously captured selfie in seconds with a very high level of identity assurance.
Cross-Platform Portability
Since biometric templates can be created on almost any device with a camera, true cross-platform biometric authentication is now possible — users can enroll using a laptop webcam and authenticate later from a smartphone or tablet. This means it’s now possible to use face authentication for everything from unlocking a car door to performing a secure password reset to accessing your bank account.
Why Choose Facial Authentication Over Facial Recognition?
For consumers and businesses alike, facial authentication is a win-win. Unlike facial recognition systems which are often performed without the user’s consent, facial authentication is permission-based and provides high levels of security to a user while letting them seamlessly access their own accounts or devices. The elegance of facial authentication is that the user does not need to be subjected to the entire identity proofing process — they just need to take a new selfie when then log into their favorite app.
For businesses, facial authentication solutions help ensure that only legitimate users are creating and accessing their online accounts — not some fraudster who has stolen the credentials or ID documents of identity theft victims off the dark web. Another key benefit of facial authentication is that businesses can leverage the same biometric data (i.e., a certified 3D face map) captured during enrollment and repurpose that same biometric for future authentication events. This means they can use the same solution for identity proofing and for ongoing user authentication.
Of course, no technology is entirely without risk. Facial recognition is highly data-intense, which can make processing and storage an obstacle. Despite enormous advances, recognizing faces from multiple camera angles or with obstructions (such as hats) is still not perfect. Plus, there have been controversies related to privacy issues, particularly in retail and government settings. This is why facial recognition should not be used for identity proofing, but instead leveraged with multifactor methods (i.e., facial authentication) to strengthen user access.
Jumio Authentication is at the Forefront of Face-Based Biometrics
Jumio uses artificial intelligence, face-based biometrics, certified liveness detection and machine learning to help organizations accurately and efficiently identify and authenticate users.
Jumio Authentication is the first solution on the market that leverages face-based biometrics for initial identity proofing and ongoing user authentication — creating an online experience that is fast, secure, accurate and easy to use. This authentication method is ideal for account logins and high-risk scenarios. Secure facial authentication can even be used to unlock doors (rental cars), self check-in (hotels), e-learning (online test taking) and continuous security (e.g., re-verifying the identity of ride-sharing drivers on a frequent basis).
Biometric technologies including facial recognition and facial authentication represent the new wave of identity and authentication solutions. With their inherent and varied benefits, it’s important to understand the distinction between these technologies and how they can be deployed to solve your unique business challenges.
