Protect against modern fraud, such as deepfakes and injection attacks, with Jumio’s most advanced liveness detection technology.
Go beyond the standard with active illumination, a Jumio-patented technique.
Try Our Demo App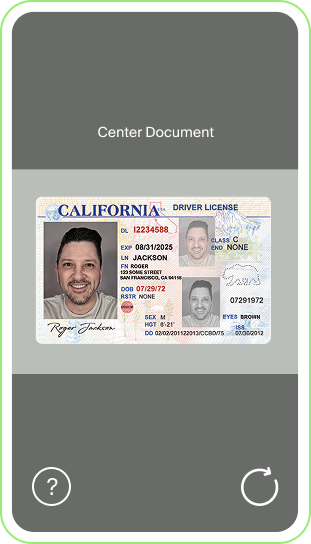

Go beyond the standard with active illumination, a Jumio-patented technique.
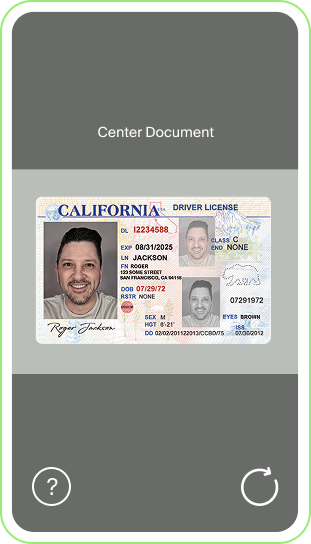
ID Check
Is the identity document (ID) authentic and valid?
1
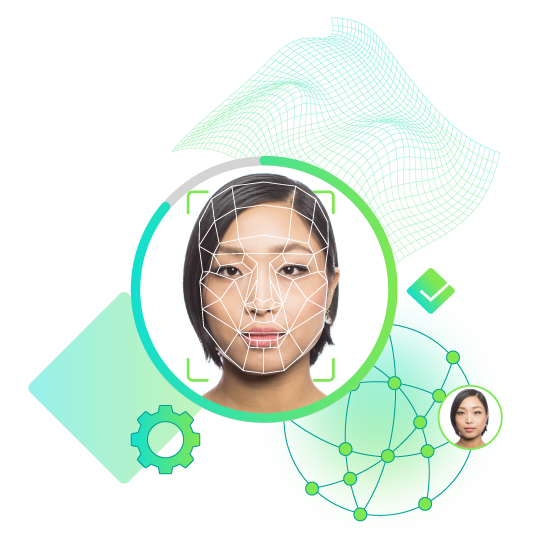
Selfie
Jumio's selfie + liveness check process verifies: Is the person holding the ID the same person shown in the ID photo? Are they physically present during the transaction? Is this a real person, not a spoof?
2

Decision
For a risk-based decision, Jumio calculates the fraud risk and approves or rejects the identity transaction in seconds based on your predefined risk tolerances.
3
Ready to see how Jumio can improve your onboarding?
Why Choose Jumio for Liveness Detection?
Patented AI-driven Technology
Jumio’s premium liveness solution uses active illumination, a patented Jumio technique, to deliver enhanced protection against deepfakes, injection attacks and presentation attacks.
Intuitive User Experience
As easy as taking a selfie, users simply center their face on the screen. Jumio’s liveness detection technology includes automated capture technology that provides real-time feedback, helping users capture optimal selfies with minimal friction. This reduces errors and improves identity verification conversions.
Advanced Selfie Technology
Our liveness technology simply requires the user to hold their mobile device at a natural angle. The solution then performs liveness and anti-spoofing detection using advanced selfie technology to ensure the user is real (not a photo, video or paper copy), is not wearing a mask and is physically present at the time of the detection.
Highly Secure
Our liveness solution has been independently tested by the NIST/NVLAP-accredited iBeta lab and achieved ISO/IEC 30107-3 Level 2 Presentation Attack Detection (PAD) conformance. This certification demonstrates resilience against advanced spoofing methods such as printed photos, screen displays, and masks.


Assurance at every step of the journey.
