Organizations often evaluate vendors on a limited set of purchase criteria (e.g., price per verification, geographic scope). At Jumio, we want to make you a smarter, savvier buyer.
Explore the following features and functionalities to learn what Jumio has to offer and what we think you should look for in a reputable solution.

Artificial intelligence (AI) and machine learning are used by many identity verification and AML solutions, so you often have to dig into their process for training the algorithms.
For identity verification, it starts with the size of their database of good and bad (fraudulent) transactions. The larger the dataset, the smarter the algorithms. Jumio’s machine learning models have been trained on hundreds of millions of real-world identity verifications to better address challenges such as blur detection, dim lighting and bad image quality.
While big data is important, you also need to have the data intelligently tagged. Jumio continually trains our machine learning models with human review to tag ID images on characteristics such as:
By tagging tens of thousands of IDs in this manner, the algorithms that feed our machine learning approach get smarter, faster and learn how to recognize these patterns automatically.

Without auditing the verification history, the only way for other verification solution providers to know if they’re getting it right is by having their customers catch and notify them of incorrect verifications. Jumio routinely audits 10%-20% of identity verification transactions to ensure our verification engine is correctly flagging fraudulent IDs and greenlighting your good customers in a timely manner. With machine learning becoming so integral, our audit serves as a powerful check to improve system accuracy.
Liveness detection enables Jumio to thwart fraudsters who are increasingly using spoofing attacks to circumvent the selfie requirement of the identity verification process. They do this by using a photo, video or a different substitute for an authorized person’s face, often with the help of rapidly evolving generative AI. Jumio’s liveness detection determines in seconds whether the user’s selfie is a live human or a fake representation while at the same time deterring many would-be cybercriminals who don’t want their actual likeness captured.


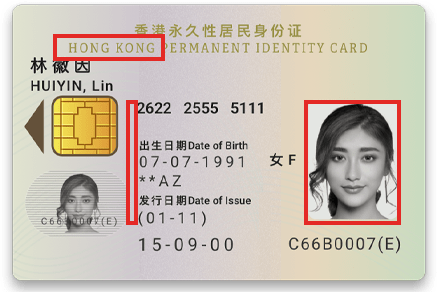
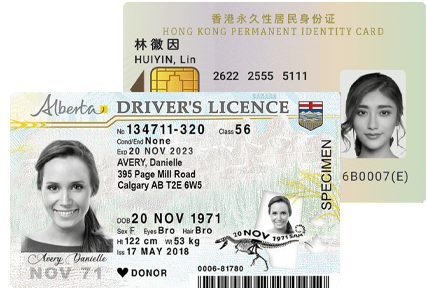
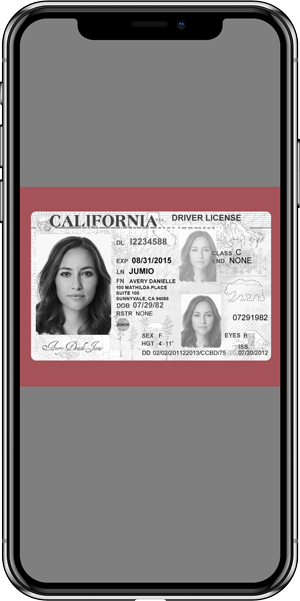
Jumio supports more than 5,000 ID document types across 200 countries and territories. It’s not just a matter of driver’s licenses and passports — Jumio supports ID cards and national IDs as well.
Jumio supports a vast array of ID subtypes including all the possible versions and permutations of each type. In some cases, there may be as many as 15 versions of a particular state’s driver’s license — some issued 5 years ago, some issued 10 years ago, some printed in landscape, some in portrait, some for commercial drivers and some for driver’s permits — each with their own unique set of security features.
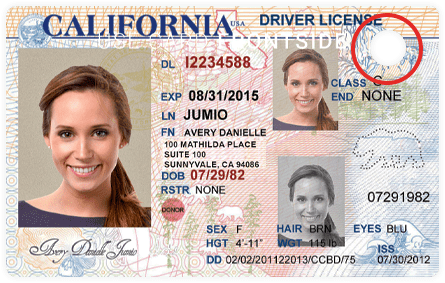
Many DMVs and passport offices use a hole punch to mark a license or passport as invalid, such as when you renew your license/passport and they punch the old one to invalidate it. A canceled and returned passport cannot be used for identification in any circumstance, including passport renewal. Unfortunately, many ID verification solutions cannot detect hole punches in driver’s licenses and passports because of the limitations of their ML algorithms. Jumio can.
Jumio helps organizations comply with Know Your Customer (KYC), Anti-Money Laundering (AML) and Bank Secrecy Act (BSA) regulations without inconveniencing customers. Jumio’s verification solutions go beyond verifying the authenticity of a government-issued ID — we confirm the live presence of the account holder. When the customer takes a selfie with their smartphone or webcam, the selfie image is compared instantly to that of the ID document tying the ID to the owner in real time, at any time and from anywhere. And our automated AML screening solution helps inform your AML risk decisions so you can keep money launderers away from your business.


When a verification fails, Jumio can provide additional information about why an ID or selfie was rejected so users can try again. Jumio returns specific and highly actionable rejection reasons which enable our customers’ end users to course correct, address the reason for failure (e.g., a thumb was obscuring a key portion of the ID) and retake a picture of their ID. Just by giving your customers a second chance, we’re able to convert up to 20% more customers.
AI and machine learning have automated big chunks of the identity verification process, but human review provides incrementally higher levels of verification accuracy. The fact is humans can still see patterns that automation and machine learning can’t. Jumio’s verification experts are trained to render a decision even with adverse factors such as blur, glare or poor lighting, whereas purely automated solutions will generally reject those images outright, resulting in higher abandonment rates and user frustration.


The more transactions captured by an identity verification provider, the more business intelligence can be baked into their solutions and the faster these companies can identify and respond to fraud patterns. Jumio’s global scale gives us a sizable advantage in recognizing these patterns and quickly adapting our risk scoring algorithms.
Jumio supports a wide range of implementations including native mobile apps (SDK), mobile web and API-based implementations. For companies looking to cast the widest possible net, including older demographics who may not be comfortable with newer technology, it just makes sense to ensure that your identity verification solution offers the broadest number of channels to reach your end users. Many of our ID and selfie captures happen via a webcam from users who are more comfortable creating new accounts from their laptops.


Cameras embedded within today’s smartphone provide crisp, high-resolution pictures. Unfortunately, this is not true for older phones or for photos captured with many webcams. Since Jumio supports ID and selfie capture via webcams, it can alert your users/customers when the image is blurry, fuzzy or just has too much glare.
Jumio identity verification solutions can read the barcode on the backside of driver’s licenses as well as the machine readable zones (MRZ) and NFC chips on passports. A user’s first and last name, date of birth and contact details can be quickly and accurately extracted from these sources. We also alert our business customers when the barcode, MRZ or NFC chip is damaged or unreadable.

The Payment Card Industry Data Security Standard (PCI-DSS) requires companies that accept credit cards to host the data securely with a PCI-compliant hosting provider. Jumio is among a select few identity verification solution providers that are PCI-DSS compliant, which means our security policies, processes and controls have been vetted and independently tested to ensure all personally identifiable information (PII) is handled in a secure manner.
Since all legitimate IDs are issued in color, it’s important to only accept colorized IDs and be able to detect which ones are, in fact, black and white. Generally speaking, black and white images are often copies of the original ID but can be doctored. NOTE: Some government IDs may use sepia or black and white photos, but the IDs themselves are always in color. Jumio’s identity verification solutions can quickly distinguish black and white images from color images of government-issued IDs and reject them accordingly.
Quickly extract key data from supporting documents such as utility bills, credit card and bank statements that their end users have scanned via smartphone. Address information from these documents can then be corroborated against the address information on the ID documents providing an additional layer of fraud detection. Jumio Doc Proof extracts key data in seconds, even when the documents themselves are crumpled and creased. Jumio currently supports Latin-based characters (e.g., those written in English, French, Spanish and Italian).
Jumio delivers a definitive “yes” or “no” verification decision on every identity transaction. This is important because every “caution” or “maybe” requires extra manual review by a team of analysts to render a final verification decision. Just as important, Jumio returns additional information about why an ID was rejected (e.g., if the user took a photo of a computer screen instead of a physical ID) or why a selfie was not accepted (e.g., if the selfie is actually a photo cropped from the physical ID). Without a simple “yes” or “no” solution, good users would be rejected without being given the chance to course correct.